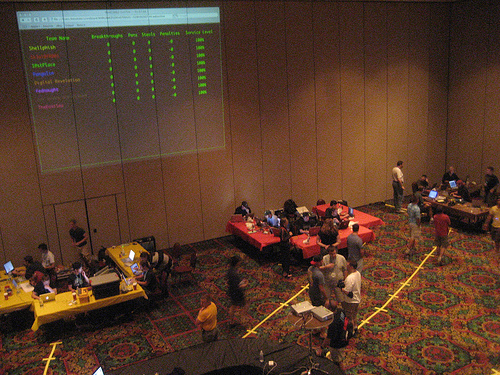
CTF 2006 Overview
Each team has a color-coded table. The
tables are set up in a "U" shape, with the open end facing the wall. The
organizers, Kenshoto, are at the center of the room at their circular black
table, and had run cables to each of the teams' tables.
Two cables are RJ45 (same as last year), and one cable is RJ11 (uh-oh).
One of the RJ45s is an uplink to a switch, and the "team LAN". The
network was 192.168.TEAM.0/24. For example, team 3 is on 192.168.3.0/24,
with a default route of 192.168.3.1.
Each team is given access to a "team server" (on the "team LAN" as
192.168.TEAM.2) with an "admin" account as well as the "root" password.
Many vulnerable services are running here, and it is the center of the contest.
The second RJ45 is a mirror port, showing all network traffic
into and out of the server. This is to allow network sniffing so that
what is happening on the server can be watched at the network level.
Unfortunately, this cable wasn't live until late Saturday. Traffic is
all source NAT'd, so it isn't possible to distinguish traffic
sources to tell a rival team's attack apart from a Kenshoto service poll.
The RJ11 is a regular phone line that gives each team access to the
Kenshoto phone system. You can call other teams by their team
number, press "0" for "The Hotline", or press "9" for voicemail. All
contest points that require interaction with Kenshoto is over "The Hotline" this year. A big
change from last year, which used network clients for scoring the
non-overwrite points.
On each server are a large number of services (web applications, network
services of unknown function, console applications, etc). Each server's
services are nearly identical to each other, so if a team can understand
what their own server is doing, they have an insight into what the other
teams' servers are doing.
For example, services might be a web application where you can order software,
the "finger" daemon, or a console-based "mail" too.
Within each service is a "token". It can be one of three possible kinds
of tokens: "public", "private", or "overwritten".
- A "public" token is one that is "normally" visible. It's not special
if you can see it, but if you can compromise the service, it can be
overwritten.
- A "private" token is one that is not normally visible. If you can
compromise the service in some way, you can read a private token.
Additionally, some private tokens can also be overwritten.
- An "overwritten" token is one where a rival team has taken their "team
token" and placed it in another team's vulnerable service.
Last year, tokens were a long string of alphanumeric characters (base64 encoding).
This year, tokens were a 32 character string of digits (base10 encoding). Each team is
given a different "team token" to use for overwrites.
To keep the teams from just turning off their server and declaring
themselves immune to attack, Kenshoto polls each of the teams' services,
and keeps a running record of each team's "Service Level" (SL). This is
a percentage of "successful polls" vs "total polls". The idea being
that as a team tries to work to patch their vulnerable services, if
they accidentally make the service non-functional, their SL will drop.
Also, outside attackers may accidentally disrupt a service while trying
to gain access to it.
By default, each of the servers pass all Kenshoto service polls, so at
the start of the contest, every team has a 100% SL.
During each Kenshoto scoring phase, Kenshoto also updates all the "private"
tokens with new token values. As the contest goes forward, a team can repeatedly
steal tokens from vulnerable services, getting more and more unique tokens.
The contest is scored based on "Breakthroughs", "Steals", "Pwns", and
"Service Level". ("Penalties" can also be levied for breaking rules,
etc.)
To earn a "Breakthrough", a team must write up a description of a vulnerable
service, and include detailed information on how to exploit its vulnerability,
and submit it to Kenshoto.
Only software vulnerabilities that give access to either private tokens or
allow for overwrites to happen are considered "valid" Breakthroughs.
To earn a "Steal", a team must exploit a vulnerable service and record a
private token. To prove that they saw a private token, the team must
submit the token to Kenshoto for scoring.
To earn a "Pwn", a team must exploit a vulnerable service and overwrite the
service's token with the "team token". Kenshoto is monitoring token locations
and automatically notices when a service token has been overwritten by a
rival team.
If a team does something against the contest rules (like performing any kind
of intentional Denial of Service), Kenshoto "fines" them with Penalty points.
Total score is ( SUM(BT values) + Steals + Pwns ) * SL - Penalties.
The tricky issue with scoring is that BT points are not public, and are not
reflected on the visible scoreboard. Each service has an associated
BT value, depending on how hard Kenshoto thinks it is to find and exploit
a given service. For example, finding how to exploit a network service that
accidentally runs commands following a ';', is going to have a small BT value. Finding how to exploit a flaw in a network protocol specifically designed to be
obfuscated is going to be worth a great deal more.
To submit a BT, the team has to put a text file with an all-numeric name
into their server's "/bt" directory, and then dial the Kenshoto Hotline
to submit the BT. For example, after putting the write-up in /bt/0003,
a team would pick up the phone:
[dial tone]
0
"Welcome to the Hotline.
Press 1 to check service levels.
Press 2 to submit a token.
Press 3 to submit a breakthrough."
3
"Welcome [team name].
Press 1 for instructions.
Press 2 to submit a breakthrough.
Press 3 to check on the status of a breakthrough."
2
"Enter the filename of your breakthrough,
followed by the pound sign."
0003#
"Your breakthrough has been accepted."
[fast busy]
To submit a stolen token, the team has to dial the Kenshoto Hotline and
enter it:
[dial tone]
0
"Welcome to the Hotline..."
2
"Welcome [team name].
Please enter your token now."
2615329583703859309184937583920631
"Token accepted.
Press 1 to submit another token."
[fast busy]
If the token isn't valid, then it responds with "Access Denied"
instead of "Token accepted". If you try to submit a token that had
already been accepted, it reports "Token previously accepted."
The contest is intended to be about measuring hacking skill.
To make sure things stay on course, Kenshoto makes several rules clear:
- No intentional denial of service (electronic, physical, psychological, anything). If someone breaks a service in the process of trying to gain access to it, that's not considered intentional. (Though Kenshoto has designed the services to be resilient, so this is uncommon.)
- Unlimited team size, but only 10 people at a time are allowed at a given team's table (fire marshal will shut down CTF if it gets crowded). This count includes groupies and visitors.
CTF 2006