This year,
Kenshoto hosted the 2007
DefCon Capture-the-Flag
Qualifications
round, starting the evening of June 1st.
The Underminers (secretly Team 1@stPlace: @tlas, drb, fury, jrod,
mezzendo, plato, psifertex, shiruken, wrffr), while having an automatic
spot in 2007 CTF, decided to play along with quals because it always
kicks so much ass. We hope our write-ups on this site will help anyone
interested in practicing or learning more for future CTF adventures.
Please send any errors, corrections, ideas, or flames to
Doc Brown.
(Thanks to Luwenth, sk3wlm4st3r, Squires, and RacerX for updates, and
additional giant thanks to sk3wlm4st3r for the BinLeet 500 walk-through, adc for the Pwnage 400 walk-through, and
to RacerX for the Pwnage 500 walk-through.)
Huge thanks to Kenshoto for letting us distribute the Web Hacking and
Pwnage 100 server
sources. Any links below marked "Kenshoto Source" were given out
after
the quals, but they're handy for recreating the services locally now that
their servers are offline.
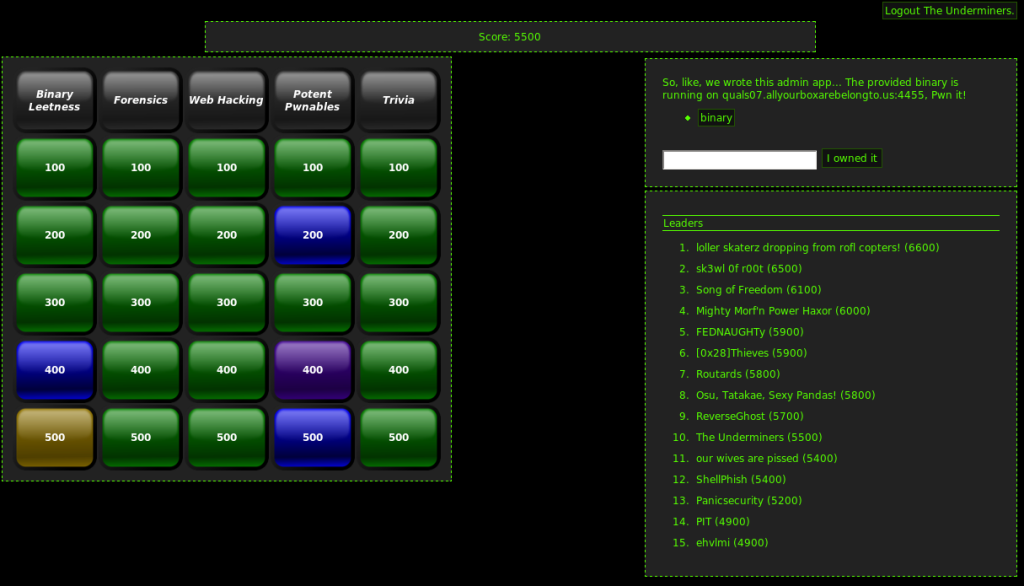
Kenshoto sent
official instructions, but
the short version is: find a secret key associated with each challenge.
Below is the list of challenges, broken down by category, along with the
key that that was recovered once the challenge was solved so you can check
your work. Questions were made available by having the team with the highest
score select a new question to work on, forcing a certain level of serialization.
For challenges that require
a running server instance (e.g. Web, Pwnables, and some Binary Leetness)
you'll use the server at *.allyourboxarebelongto.us. These services
may or may not be available, depending on Kenshoto's infrastructure. If
there is source available, you can run your own copy.
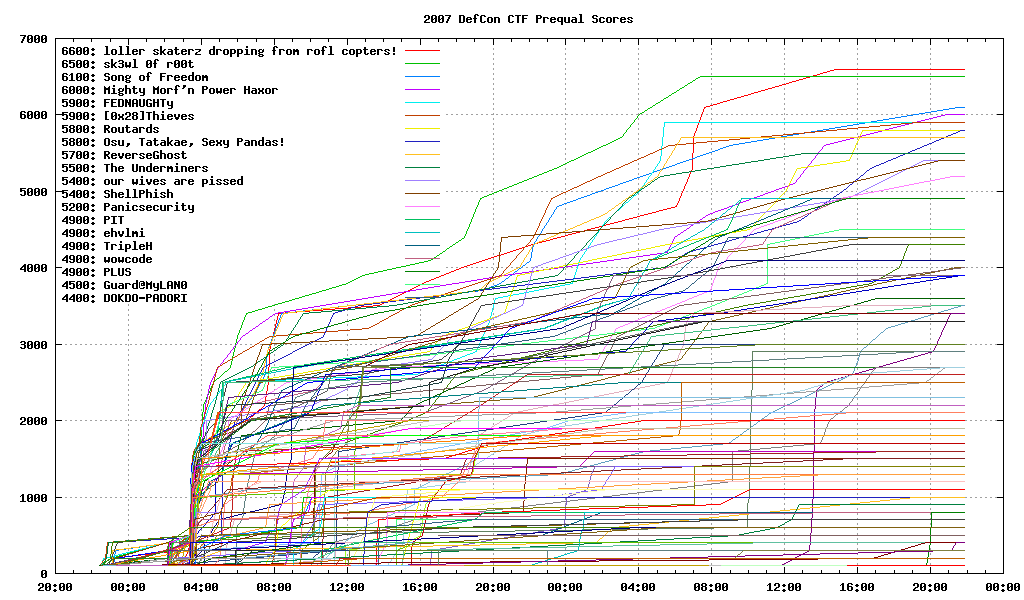
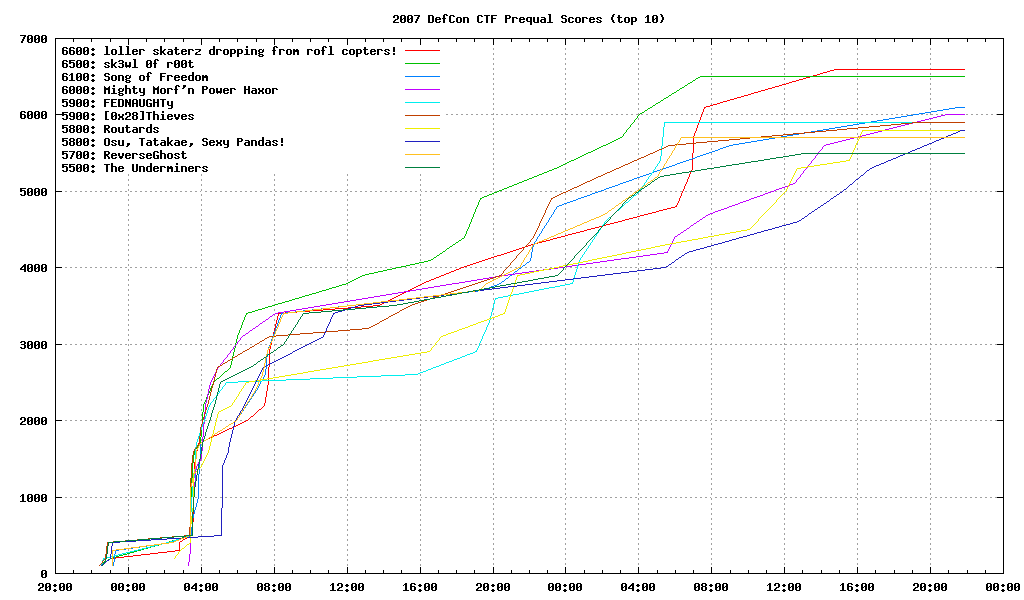
The walk-throughs are not finished; we're still waiting on Kenshoto to give us all the pwnage. In the meantime, here are some plots of scores, based on the
raw scoring data: